Disclaimer: This article is for informational purposes only and does not constitute legal advice. We recommend consulting with a qualified compliance expert or legal counsel to address your specific situation.
Managing a healthcare practice or health-tech company is already complex. The added weight of potential multi-million dollar HIPAA fines and the constant threat of cyberattacks can be overwhelming. HIPAA Compliance is the process of adhering to the U.S. federal standards for protecting sensitive patient data, known as Protected Health Information (PHI), from being disclosed without consent. It involves a set of technical, administrative, and physical rules that healthcare entities and their business partners must follow. If intricate regulations and evolving security risks leave you unsure where to begin, this guide is designed for you. We will break down everything you need to know about HIPAA compliance and data security into practical, actionable steps for 2026, transforming it from a burden into a business advantage.
Understanding HIPAA Fundamentals: The What and Who
The Health Insurance Portability and Accountability Act (HIPAA) of 1996 is a US federal law that created national standards to protect sensitive patient health information. This information is called Protected Health Information (PHI), or ePHI when in electronic form. Think of HIPAA as the rulebook that ensures patient data is kept private and secure, which is fundamental to building patient trust. For your business, compliance isn’t just about avoiding fines; it’s about demonstrating your commitment to patient privacy, a key differentiator in a competitive market.
Who Must Comply with HIPAA Rules?
- Covered Entities: These are the frontline healthcare organizations. This category includes health plans (like insurance companies), healthcare clearinghouses, and healthcare providers who electronically transmit health information (like doctors’ offices, clinics, hospitals, and pharmacies).
- Business Associates: This category includes any vendor or subcontractor that creates, receives, maintains, or transmits PHI on behalf of a Covered Entity. This could be an IT provider, a cloud storage service, a billing company, or even a service like Care VMA’s Virtual Medical Assistants.
What Information is Protected? A Breakdown of Protected Health Information (PHI)
PHI is any individually identifiable health information. The U.S. Department of Health & Human Services specifies 18 identifiers that make health information PHI. If a piece of data is linked to any of these, it must be protected under HIPAA.
Common PHI Identifiers Include:

- Names
- All geographic subdivisions smaller than a state
- All elements of dates (except year) directly related to an individual
- Telephone numbers
- Fax numbers
- Email addresses
- Social Security numbers
- Medical record numbers
- Health plan beneficiary numbers
- Account numbers
- Biometric identifiers, including finger and voice prints
- Full face photographic images
The Three Core HIPAA Rules You Must Master
HIPAA is primarily divided into three main rules that dictate how PHI must be handled. Mastering these is non-negotiable for compliance.
The HIPAA Privacy Rule: Patient Rights and Data Use Limitations
The Privacy Rule sets the standards for who can access and use PHI. It empowers patients by giving them rights over their own health information, including the right to examine and obtain a copy of their health records and to request corrections. For your practice, this rule defines how you can use PHI for treatment, payment, and operations, and when you must get explicit patient authorization for other disclosures.
The HIPAA Security Rule: Your Digital Data Fortress
The Security Rule focuses specifically on protecting ePHI. It requires organizations to implement three types of safeguards to ensure the confidentiality, integrity, and availability of electronic data.
- Administrative Safeguards: These are the human-focused policies and procedures. It includes conducting a security risk analysis, designating a security officer, implementing security training for all staff, and having a plan for managing security incidents.
- Physical Safeguards: These controls protect your physical hardware and facilities. This means securing server rooms, controlling access to workstations, and having policies for the use of mobile devices and electronic media like USB drives.
- Technical Safeguards: These are the technology-based protections. Key requirements include access control (ensuring users only see the data they are authorized to see), audit controls (logging access and activity), integrity controls (preventing improper alteration or destruction of ePHI), and transmission security (encrypting ePHI when sent over a network).
The HIPAA Breach Notification Rule: Mandatory Steps After a Data Leak
This rule requires Covered Entities and Business Associates to provide notification following a breach of unsecured PHI. Depending on the size of the breach, notifications may need to be sent to affected individuals, the media, and the Secretary of Health and Human Services. Having a clear, documented breach response plan is a critical component of compliance.
Practical Strategy for Achieving and Maintaining HIPAA Compliance in 2026
Viewing HIPAA as a checklist to avoid penalties is a reactive mindset. The forward-thinking approach is to see compliance as a strategic framework for building a resilient, trustworthy, and efficient practice.
The First Step: Conducting Self-Audits and Risk Assessments
The cornerstone of any HIPAA compliance program is a thorough risk assessment. This goes beyond a simple IT security scan. It’s a comprehensive review of your administrative, physical, and technical safeguards to identify potential risks and vulnerabilities to PHI. A proper assessment helps you prioritize your remediation efforts and document your due diligence, which is critical if you are ever investigated. This process is key to your overall Clinic Workflow Optimization: Cut Errors & Admin Load [2026].
Developing Policies, Procedures, and Training Your Team
Your policies are the “what” and “why” of your compliance program, and procedures are the “how.” Every team member, from the lead physician to the Virtual Assistant Receptionist to Reduce Call Wait Time and Build Patient Trust, has a role in protecting PHI. Regular, documented training is mandatory. It ensures your staff understands the policies, recognizes potential threats like phishing scams, and knows how to respond to incidents, creating a human firewall as your first line of defense.
From Annual Audits to Continuous Monitoring: The Proactive Approach
Many practices mistakenly believe a single annual audit is sufficient. However, in today’s threat landscape, this is like checking the locks on your house only once a year. Threats evolve daily. A proactive approach involves continuous monitoring of your systems. This modern strategy allows for real-time detection of suspicious activity, helping you prevent a potential incident from becoming a catastrophic breach. According to an IBM report, the average time to identify and contain a data breach is 277 days. Continuous monitoring drastically reduces this window, saving you money, time, and reputational damage.
Consequences of HIPAA Violations: More Than Just Fines
The consequences of non-compliance extend far beyond a financial slap on the wrist. They can threaten the very existence of a practice.
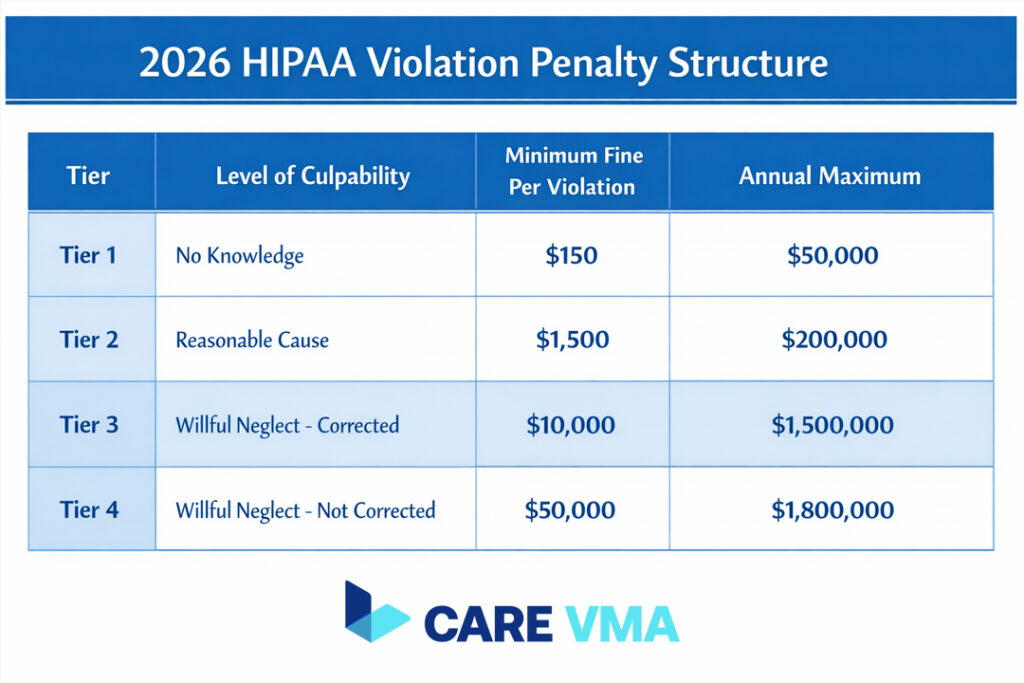
The Latest Financial Penalty Structure
Penalties are tiered based on the level of negligence and can be staggering. The Office for Civil Rights (OCR) adjusts these amounts for inflation.
HIPAA Penalty Tiers for 2026 (Example Structure):
- Tier 1 (Lack of Knowledge): Minimum fine of $137 per violation, up to $34,464.
- Tier 2 (Reasonable Cause): Minimum fine of $1,379 per violation, up to $68,928.
- Tier 3 (Willful Neglect – Corrected): Minimum fine of $13,785 per violation, up to $68,928.
- Tier 4 (Willful Neglect – Not Corrected): Minimum fine of $68,928 per violation. The maximum penalty is $2,067,813 per year for each violation category.
Reputational Damage and Loss of Patient Trust
Perhaps the most damaging consequence is the loss of patient trust. A breach is a public event. It erodes patient confidence and can lead them to seek care elsewhere. Rebuilding a practice’s reputation after a major breach is an expensive and arduous journey. Being known as a secure and trustworthy provider is a powerful asset.
FAQ (Frequently Asked Questions About HIPAA Compliance)
Is using standard WhatsApp for patient communication a HIPAA violation?
Yes, using the standard version of WhatsApp is a violation. HIPAA requires end-to-end encrypted communication platforms that will also sign a Business Associate Agreement (BAA). Standard consumer messaging apps like WhatsApp, Facebook Messenger, or iMessage do not offer BAAs and are not compliant.
My clinic is small. Do I still need to follow all the complex HIPAA rules?
Yes, the rules apply to all Covered Entities, regardless of size. However, HIPAA is designed to be scalable. This means the specific safeguards you implement can be tailored to the size, complexity, and resources of your organization, as determined by your risk assessment.
What is the main difference between HIPAA and GDPR?
HIPAA is a U.S. law specifically regulating Protected Health Information. The General Data Protection Regulation (GDPR) is a comprehensive data privacy law in the European Union that applies to all personal data of EU citizens, not just health information. While they share principles like data protection and privacy, their scope, jurisdiction, and specific requirements are different.
Conclusion & Next Steps
Achieving HIPAA compliance is not a one-time project; it is an ongoing commitment that forms the foundation of a modern, secure, and trustworthy healthcare practice. By shifting your perspective from viewing HIPAA as a regulatory burden to an investment in patient trust and operational resilience, you create a powerful competitive advantage. It signals to your patients and partners that you value their privacy as much as you value their health.
Feeling overwhelmed? You do not have to navigate the complexities of HIPAA compliance alone. The right systems and support can streamline the entire process, ensuring you are not only compliant but also more efficient. Our Virtual Medical Assistant Services are built on a foundation of security and compliance, freeing you to focus on patient care. Schedule a free consultation with our healthcare data security experts at Care VMA to map your path to full compliance and peace of mind.


